AI authorization
Policy-based guardrails for agents
Secure agentic workflows, RAG pipelines, and MCP servers with policy-driven access control and full decision logging.
Security
Engineering
Compliance
Reduce hidden AI access risks
Remove fragmented, in-code authorization that creates blind spots and over-privileged AI.
Control authorization logic
Define, approve, and update policies in one place for agents, users, and services.
See and stop AI access instantly
Use an AI agent kill switch to revoke access in real time. See exactly what each agent is allowed to access.
Build your AI security strategy
Control access for every identity, at any scale
Enforce fine-grained, contextual authorization across apps, APIs, services, and AI systems from a centralized control layer.
Launch production-ready AI systems with Cerbos
Identity systems establish who someone is. Cerbos controls what they are allowed to do, at the moment decisions are enforced.
1
Every action is checked
When a user clicks a button, a service calls an API, or an AI agent uses a tool, the request is sent to Cerbos.
2
The request is evaluated
Cerbos reviews who is making the request, what they want to do, what they want to access, and the surrounding context.
3
The decision is enforced
Cerbos returns ALLOW or DENY. The application follows that decision before the action runs.
Access control for AI agents and every other use case
Cerbos is an authorization management platform that scales with your business.
Enterprise app authorization
Authorization software that scales with your business
ABAC
RBAC
ReBAC
PBAC
Runtime
Event-time
Admin-time
Audit-time
Cloud
Self-hosted
On-premise
Air-gapped
Weak authorization is how breaches start. AI scales the mistake.
Over-permissioned access
AI agents and services can do more than they should. One mistake can expose sensitive data or trigger unauthorized actions.
Gaps between systems
When access rules live in different services, decisions become inconsistent. Attackers exploit those gaps.
Access that never expires
Long-lived tokens and shared credentials stay valid long after they are needed, increasing the chance of compromise.
No way to stop it instantly
If an agent goes beyond its scope, access continues until someone rotates credentials or restarts systems.
Become compliance-ready with every access decision, AI or human
SOC 2
SOC 3

HIPAA
ISO 27001

GDPR
FedRAMP
PCI DSS
SOC 2
SOC 3

HIPAA
ISO 27001

GDPR
FedRAMP
PCI DSS
Capture every decision for all identities
Log requests, actions, resources, access outcomes, and service-to-service authorization calls for both humans and machines.
Trace policy lineage
See the exact policy, version, and release behind each decision for complete traceability.
Monitor with context
Review detailed logs, policy versions, and real-time metrics across all PDPs and environments.
Simplify audits and compliance
Maintain centralized, structured logs on-premise to support audits and demonstrate readiness for FedRAMP, SOC 2&3, ISO 27001, HIPAA, PCI DSS, and GDPR.
Plug into your existing stack
Go live with authorization in one sprint
MCPs
Integrate Cerbos authorization with Fasten MCP and Anthropic MCP to control agent workflows at the orchestration layer.
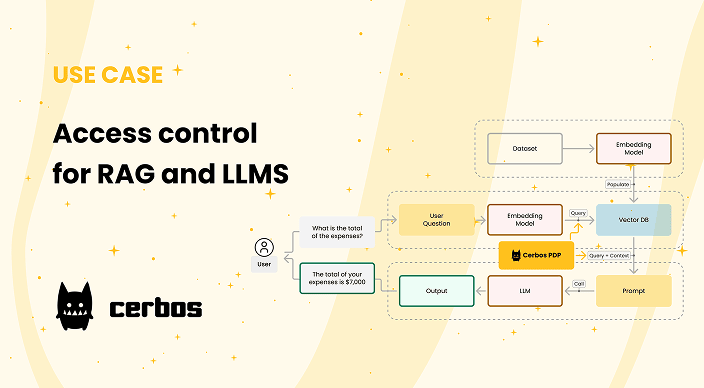
Vector stores
Enforce policy-based access for embeddings and retrievals across FAISS, Pinecone, Weaviate, Chroma, and Qdrant.
AI infrastructure
Deploy Cerbos policies alongside your AI model APIs. Works with OpenAI, Anthropic, Groq, and other inference providers.
SDKs
Use Cerbos SDKs for languages like JS, Python, Go, Rust, Java, and .NET to authorize requests from your application code.


Implementing Zero Trust with Cerbos
Why engineering teams love Cerbos
Recognized by the community
Award-winning technology, built for security and scale
With a strong open source foundation, active AuthZen membership, and multiple industry awards, Cerbos has been recognized as a secure and reliable authorization software since 2021.
Hackernoon Startup Awards 2025
Startups 100 Index 2025
API World 2025 Awards
Intellyx Digital Innovator 2023
Purpose-built authorization, not a generic policy engine
Generic policy engines | Cerbos Hub | |
|---|---|---|
Policy language General-purpose policy languages designed for broader use cases. | Policy language YAML policies purpose-built for authorization, readable by security teams. | |
Authorization model Authorization patterns must be assembled from generic primitives. | Authorization model First-class RBAC, ABAC, and PBAC with principal/resource/action semantics. | |
Evaluation latency Varies by policy complexity and engine architecture. | Evaluation latency Sub-millisecond, optimized for per-request evaluation at machine speed. | |
Policy lifecycle Custom sync, manual distribution, separate CI/CD tooling. | Policy lifecycle Cerbos Hub: managed policy lifecycle with CI/CD, testing, and real-time distribution. | |
Audit and compliance Decision logs require additional infrastructure to capture and correlate. | Audit and compliance Structured decision logs with policy version lineage, built in. |
Learn more about AI security
Article
Governing AI coding agents with Cerbos Synapse

Ebook
Securing AI agents and non-human identities in enterprises
Ebook
Zero Trust for AI: Securing MCP Servers
Article
Implementing authorization in RAG-based AI systems with Cerbos
Authorization for enterprise software and AI
Externalized, policy-based, runtime authorization for your apps, enterprise software, AI systems and workflows.
Authorization for AI systems
By industry
By business requirement
Useful links
What is Cerbos?
Cerbos is an end-to-end enterprise authorization software for Zero Trust environments and AI-powered systems. It enforces fine-grained, contextual, and continuous authorization across apps, APIs, AI agents, MCP servers, services, and workloads.
Cerbos consists of an open-source Policy Decision Point, Enforcement Point integrations, and a centrally managed Policy Administration Plane (Cerbos Hub) that coordinates unified policy-based authorization across your architecture. Enforce least privilege & maintain full visibility into access decisions with Cerbos authorization.
