Implement authorization once
Replace complicated authorization logic with a single API call and allow product owners and security teams to manage access without touching code.
Engineering
Product
Operations
Implement once, enforce everywhere
Replace scattered if/else permission blocks with a single Cerbos SDK call. Define access in policy, enforce it across every app, API, and AI agent - without reimplementing logic per service.
Plugs into your existing stack
Native SDKs for Go, Node, Python, Java, .NET, Rust, PHP, and Ruby and more. Integrates with your identity provider, API gateway, and CI/CD pipeline. No new infrastructure to learn.
Offload policy management
Let product owners and security teams manage roles, permissions, and tenant rules through Cerbos. You implement authorization once - they handle ongoing changes without touching code.
“What caught our attention was the deployment modes of Cerbos, which were very adherent to our new infrastructure running Kubernetes. We could choose to run as a server or as a sidecar. And it was focused on performance and easier to integrate than other solutions out there because Cerbos uses JSON or YAML; you choose.”

Paulo Henrique Pereira Cardoso, Tech Manager
Implement once, enforce everywhere
Replace scattered if/else permission blocks with a single Cerbos SDK call. Define access in policy, enforce it across every app, API, and AI agent - without reimplementing logic per service.
Plugs into your existing stack
Native SDKs for Go, Node, Python, Java, .NET, Rust, PHP, and Ruby and more. Integrates with your identity provider, API gateway, and CI/CD pipeline. No new infrastructure to learn.
Offload policy management
Let product owners and security teams manage roles, permissions, and tenant rules through Cerbos. You implement authorization once - they handle ongoing changes without touching code.
“What caught our attention was the deployment modes of Cerbos, which were very adherent to our new infrastructure running Kubernetes. We could choose to run as a server or as a sidecar. And it was focused on performance and easier to integrate than other solutions out there because Cerbos uses JSON or YAML; you choose.”

Paulo Henrique Pereira Cardoso, Tech Manager
Update access logic without engineering sprints
Product owners update roles, permissions, and tenant-specific rules through Cerbos - no code deploys, no waiting on engineering.
Support any access model your customers need
RBAC, ABAC, PBAC, multi-tenancy, custom roles - meet enterprise buyer requirements without building from scratch.
Unblock your roadmap from IAM bottlenecks
Stop losing sprints to authorization rework. Cerbos externalizes access control from product code so your team stays focused on what matters.
“Having the separation of the permissions from the code base just makes the code base more elegant. It means they're not tied to specific endpoints. And ultimately it means that different business owners have the ability to actually make updates.”

Henry Arnold, CTO & Co-Founder, Nook

Ship policy changes through your CI/CD
Deploy authorization updates through your existing Git and CI/CD workflow. No manual steps, no separate deployment pipeline.
Full visibility into every access decision
Log requests, actions, resources, and authorization decisions across all services - human and machine.
Stay audit-ready without the fire drill
Centralized, structured logs simplify compliance cycles for SOC 2, ISO 27001, HIPAA, PCI DSS, and GDPR.
“One of our favorite features is the audit logs because they allow us to understand what's happening inside the black box. This level of visibility gives us confidence in our security posture.”

Rob Crowe, Principal Engineer
How in-house authorization becomes your bottleneck
Whether you built it from scratch or it's buried in your application code, the result is the same: scattered logic, constant rewrites, and compliance work that never ends - all for a problem that's already been solved.
You're reimplementing the same logic everywhere
Authorization checks scattered across microservices, APIs, and frontend layers. Every new surface means duplicating logic, diverging behavior, and debugging inconsistencies across services.
Every change means touching code
New tenant? New role? New feature flag? Each one requires code changes, engineering review, and a full redeployment - for what should be a configuration update.
You're responsible for auditing and compliance
Hardcoded authorization means you also own the audit trail. Building logging, evidence collection, and compliance reporting from scratch - on top of the authorization logic itself.
Your authorization headache solved
Cerbos externalizes and centralizes authorization
Define your policies
Replace the spaghetti if/else case/switch code with a single function call.
Programmatic policy management
Create, update and manage policies using the Cerbos CLI or via API from your applications.
Flexible policy delivery
Deliver policies from from your existing Git provider, any CI/CD pipeline or directly from the Cerbos Hub interface.
Validate policy changes automatically
Run automated tests in Cerbos Hub's CI pipeline before deploying to your Policy Decision Points.
How Complex centralized scattered roles and permissions with Cerbos.
Consistency across services
Permissions managed from one place
Faster app iterations
“It used to be that somebody on the product team goes to change something, and we forgot to change it in 9 of 10 places. So it was always a disaster. With Cerbos, we have one repo of policies. That's all you have to worry about.”

Steve High
Staff Engineer, Complex
Cerbos authorization in action
End-to-end authorization across applications, infrastructure, and AI systems with a unified policy engine, data layer, and control plane.
Authorization management
Cerbos Hub
Policy Administration Point
Cerbos Hub is the control plane for policy authoring, testing, versioning, distribution, and audit visibility. Hub provides end-to-end policy management out of the box.
Data and Integration
Cerbos Synapse
Enrichment and Orchestration
Synapse fetches identity, resource, and relationship data from external systems to enrich authorization requests, and translates infrastructure protocols into Cerbos policy checks.
4.4k
< 1 ms decision time
Cerbos PDP
Policy Decision Point
PDP is an open source authorization engine that evaluates requests against policies and returns access decisions. It's stateless, high-performance, and built to scale horizontally.
Native SDKs
Cerbos PEP SDKs
Policy Enforcement Point
Cerbos PEPs are language-native client libraries that connect applications directly to PDPs to enforce real-time access decisions, with SDKs available for all major languages.
Implement authorization once, scale everywhere
Define access in policy, enforce it with one SDK call, and let product and security teams manage changes through Cerbos - without touching your code.
Replace scattered if/else permission blocks with a single Cerbos SDK call. Define access rules in declarative policy, reusable across every service, tenant, and environment. You implement authorization once - Cerbos handles the rest.
Developer-ready integrations
Works with your existing tools, workflows, and infrastructure
Flexible policy sources
Add policies from any Git provider, any CI/CD tool, Cerbos Hub API, cerbosctl CLI, direct UI upload.

SDKs and integration for every stack
Use SDKs for JS, Go, Python, Java, .NET, Rust, PHP, and Ruby, plus integrations for AI frameworks, vector databases, and MCP servers.


Deployment targets
Deploy to Cerbos PDPs in containers, serverless, edge, or multi-region clusters.
Compliance ready audit logs
Ensure Zero Trust, compliance and audit readiness for FedRAMP, SOC 2, SOC 3, ISO 27001, HIPAA, PCI DSS, and GDPR.

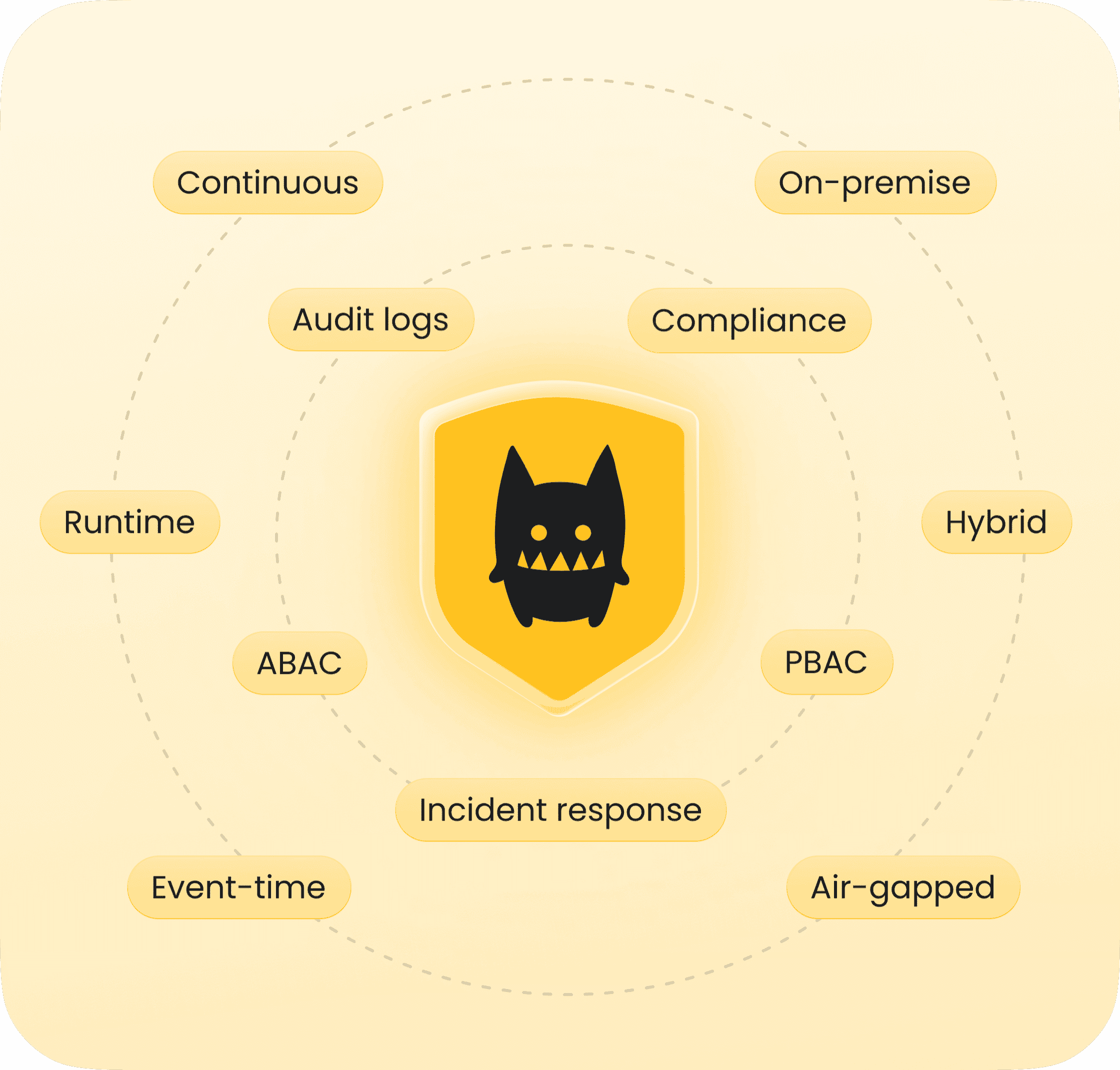
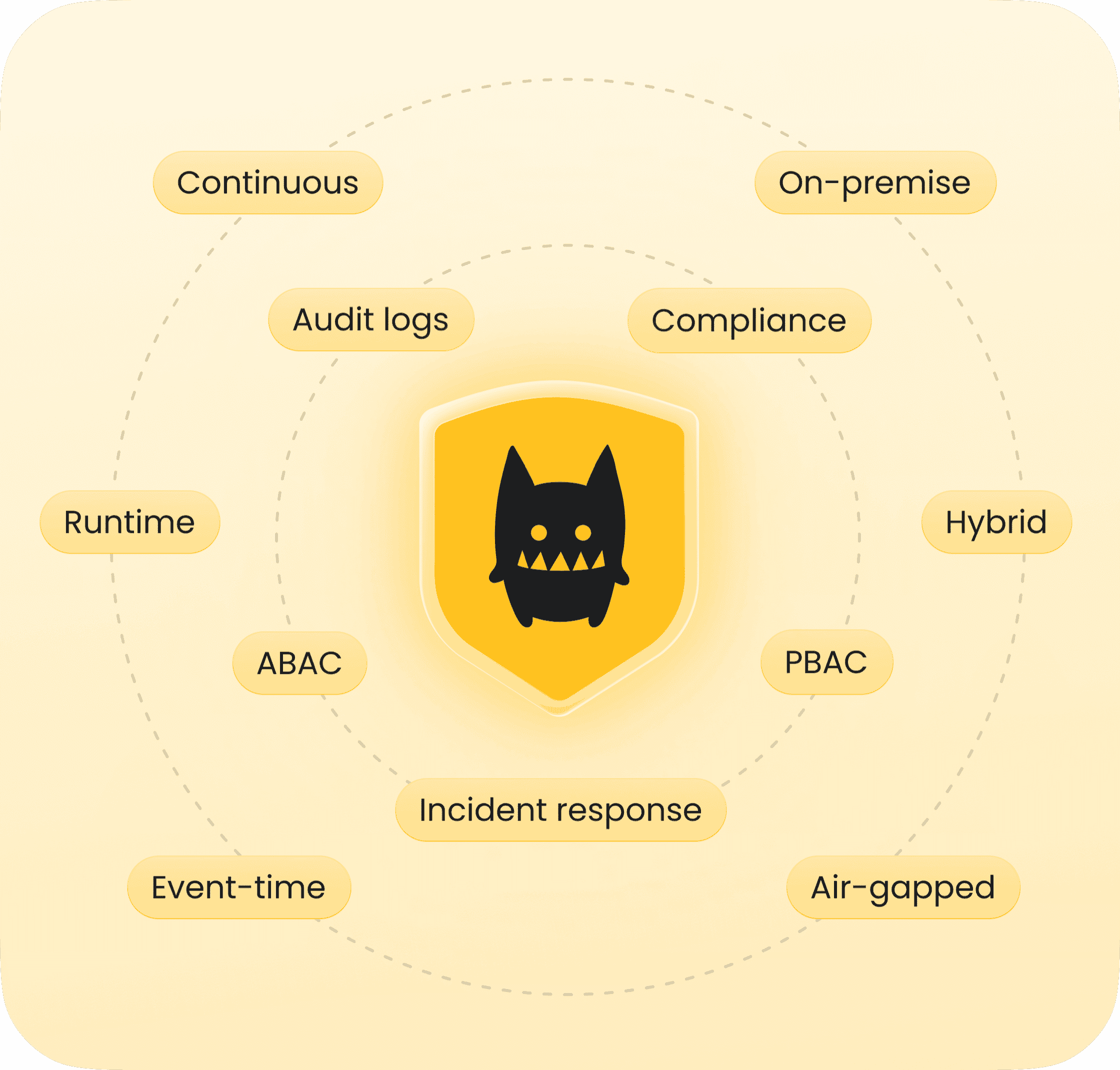
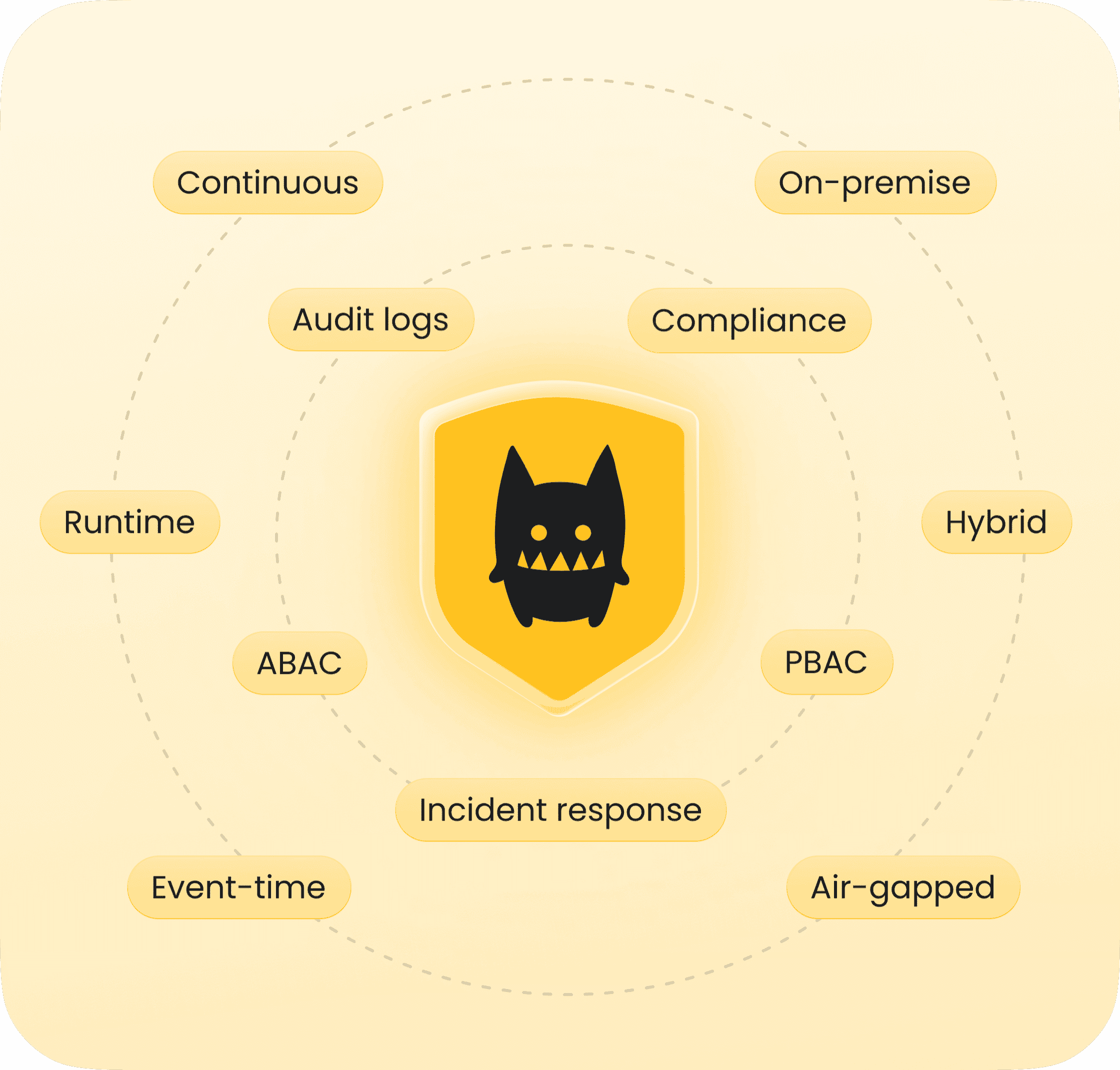
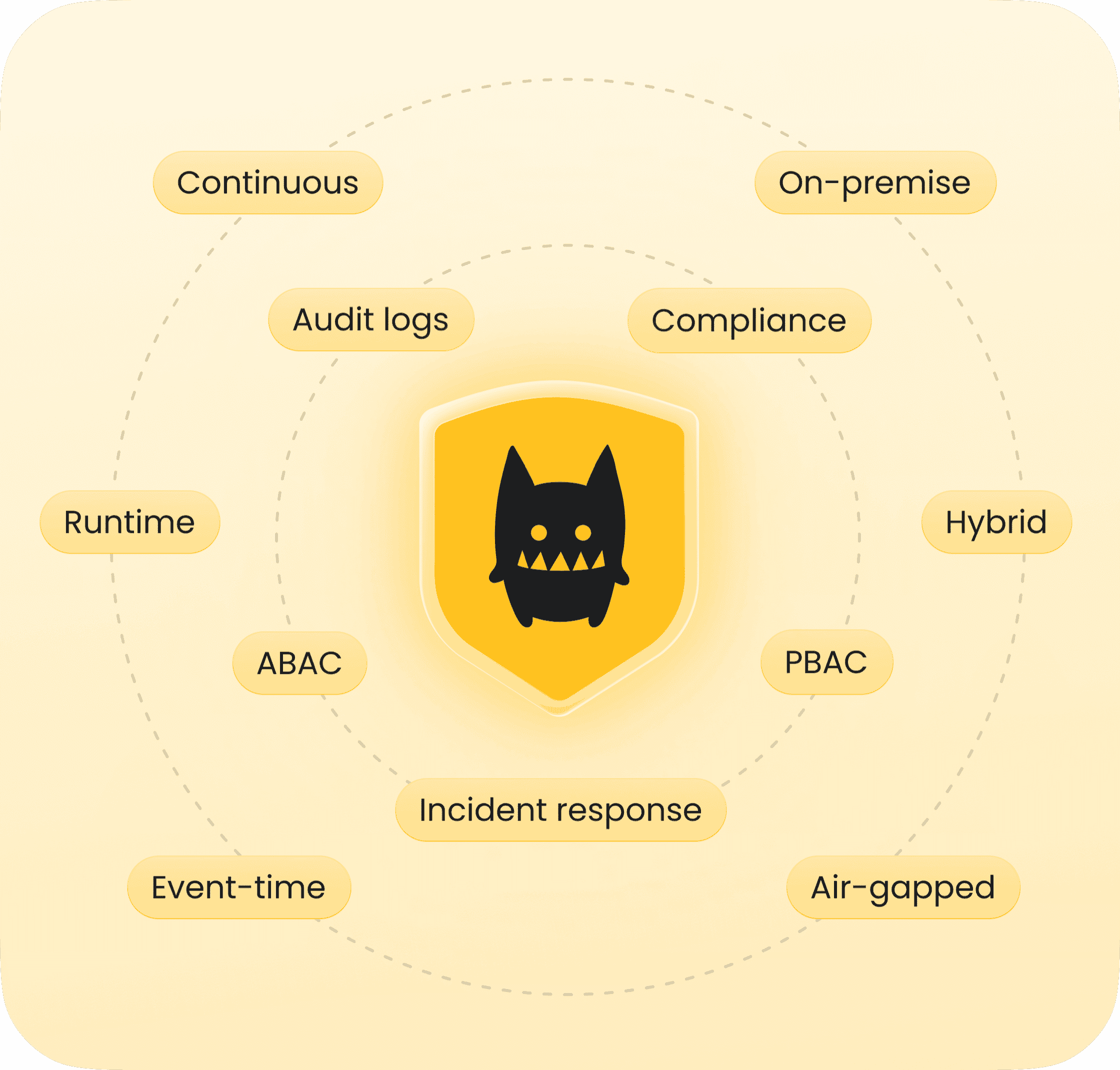
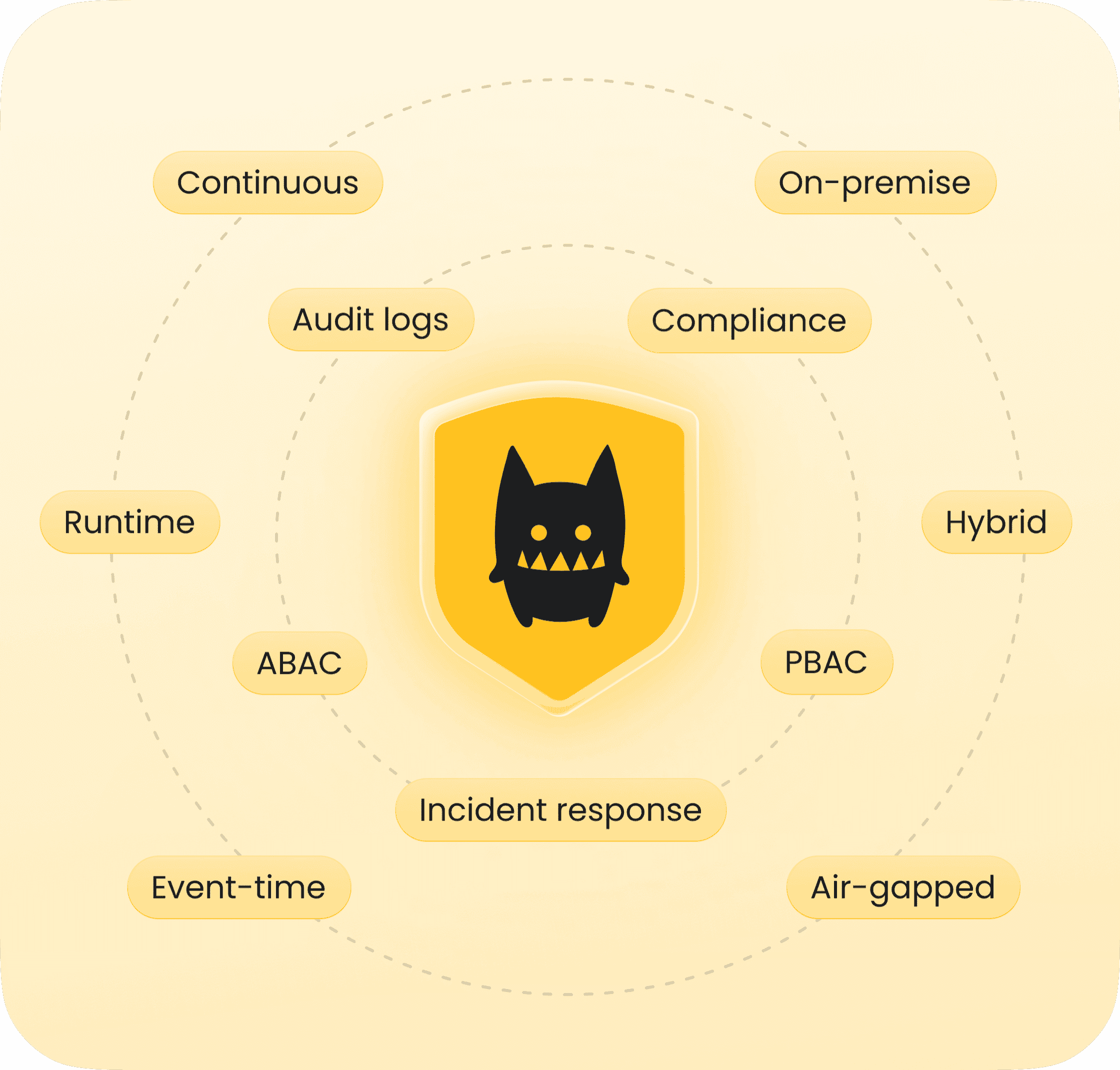
Access control for every use case
AI authorization
Enterprise authorization
ABAC
RBAC
ReBAC
PBAC
Runtime
Event-time
Admin-time
Audit-time
Legacy systems
Cloud
Self-hosted
On-premise
Air-gapped
Contextual, continuous authorization
Fine grained, contextual, continuous authorization at scale
Why engineering teams love Cerbos
Why teams love Cerbos
Resources: from quickstart to production
Guide
Mapping business requirements to authorization policy
Ebook
How to adopt externalized authorization

Guide
Agent skill for writing authorization policies
Guide
Service to service authorization
Article
Filtering data using authorization logic
Article
AI agents, the Model Context Protocol, and the future of authorization guardrails
Ready to solve your authorization headache?
See how Cerbos replaces scattered permissions logic with a single API call, and lets you hand off policy management for good.
