Tooling, Performance, .NET SDK, JS SDK, Playground - Cerbos v0.18 Release
The latest release of Cerbos, v0.18, includes performance and tooling improvements, a new .NET SDK, a major upgrade to the JavaScript SDK, and the addition of viewing the Query Plan in the Playground.
We have been working closely with users of Cerbos such as Utility Warehouse, 9fin, Salesroom, Refine, and Doorfeed on this release and can’t wait to hear more on what you would like to see in future releases - join our Slack community to join the conversation.
Tooling & Performance
Cerbos v0.18 has been focused on a number of tooling updates and optimizations.
- The
cerbosctlutility is now available as a container. It makes it easier to provision Cerbos on container orchestration systems using native constructs (for example, init containers on Kubernetes). - Cerbos now caches the verification state of JWTs in memory to avoid repeating the expensive cryptographic operations on each and every request. The tokens are still validated each time to ensure that they haven’t expired and are valid for use.
- There are several improvements to the PlanResources API.
- An optimization pass has been introduced to simplify some of the logical expressions in the query plan and eliminate redundant conditions.
- All aliases, such as
Rforrequest.resource, are expanded to their long-form in the plan output to help make the API response predictable. - The output of the
filterDebugfield in the query plan response is standardized to use S-expression format to ensure that it is easily verifiable by automated tools.
- Calls to the PlanResources API are now captured by the audit logger and written to the decision log with the full serialized request and response.
- Cerbos now reports metrics about store synchronization attempts and any failures encountered. They can be used to create alerts to detect when the policy store is drifting from the remote source due to network issues or credential expiry.
- Distributed traces received in any of W3C trace context, B3, or Baggage propagation formats are now automatically detected and handled by the Cerbos server.
- Also included are a number of other updates around how hidden directories are handled and schema ID generation when using the Admin API.
You can find the full release notes here.
.NET SDK
Continuing on from the last release, a new .NET SDK is now available via NuGet and GitHub.
The Cerbos SDKs make calling and interacting with Cerbos a much more streamlined experience and provide native methods for constructing calls out to check authorization in your codebase. As with everything else with Cerbos, they are open-source and can be found on GitHub.
Next up is a PHP SDK which will be released in the coming weeks.
JavaScript SDK
The Node SDK has been re-written from scratch to make use of a common core that is built off the protobuf definitions of the Cerbos API and implements a gRPC and HTTP client which can be used interchangeably depending on your implementation.
This revision includes methods for fetching a query plan via the PlanResources API as well as the typical authorization check.
The move to use gRPC on the server-side implementation results in a significant performance increase due to the inherently lower overhead of gRPC+protobuf over a more traditional JSON-based HTTP interface.
As this is a breaking change, the new SDK is published under @cerbos/http and @cerbos/grpc - documentation can be found on GitHub.
Playground: Query Plan
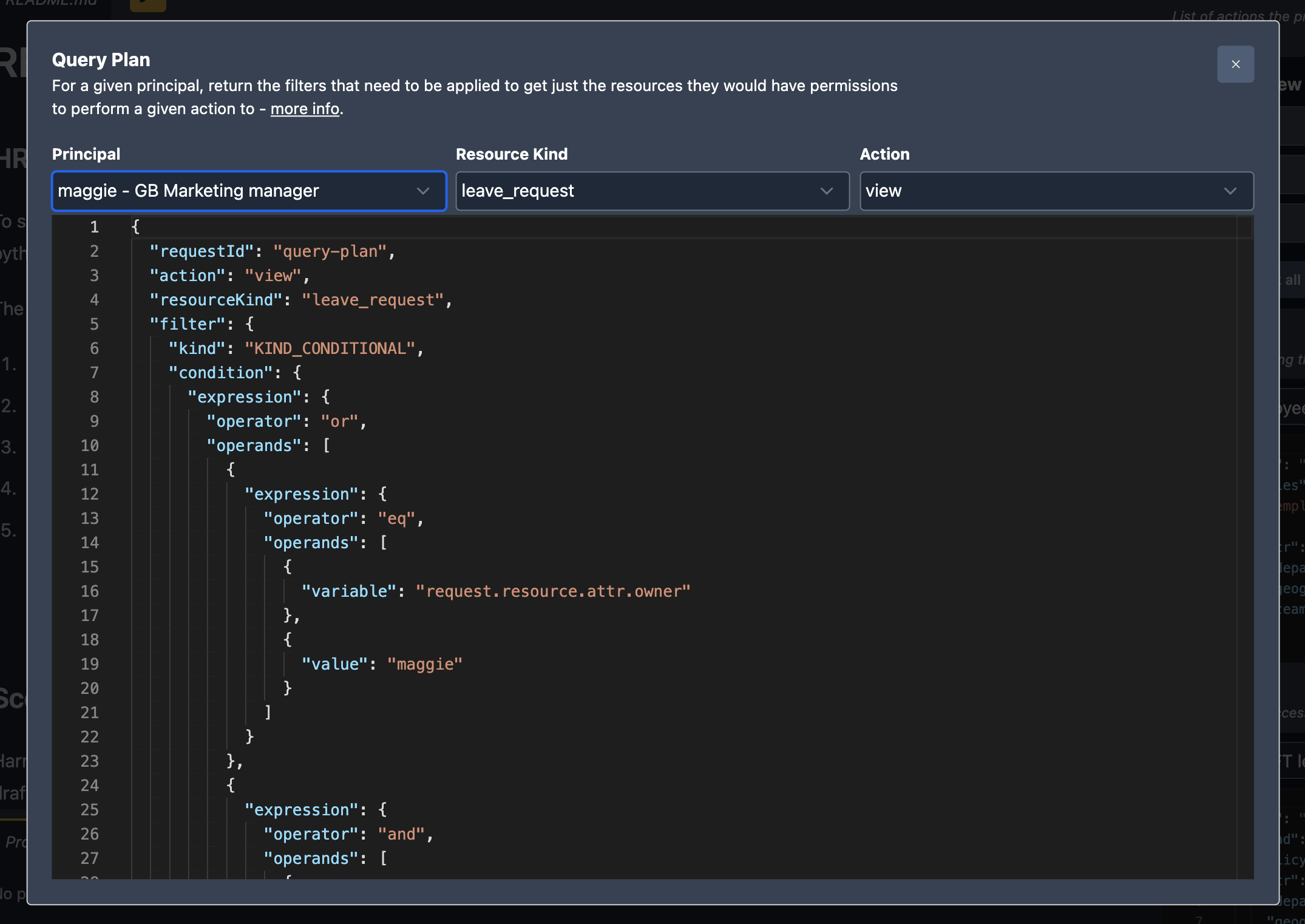
The Cerbos Playground now includes a new mode to view the query plan for a specific principal, resource kind, and action. This mode enables you to see the conditions which need to be met when fetching resources from your data storage to select only the instances that the user is authorized to access. You can find out more about query plans here.
You can find the full release notes here and if you have any questions join our Slack community.
Book a free Policy Workshop to discuss your requirements and get your first policy written by the Cerbos team
Recommended content

Mapping business requirements to authorization policy
eBook: Zero Trust for AI, securing MCP servers

Experiment, learn, and prototype with Cerbos Playground
eBook: How to adopt externalized authorization

Framework for evaluating authorization providers and solutions

Staying compliant – What you need to know
Subscribe to our newsletter
Join thousands of developers | Features and updates | 1x per month | No spam, just goodies.
Authorization for AI systems
By industry
By business requirement
Useful links
What is Cerbos?
Cerbos is an end-to-end enterprise authorization software for Zero Trust environments and AI-powered systems. It enforces fine-grained, contextual, and continuous authorization across apps, APIs, AI agents, MCP servers, services, and workloads.
Cerbos consists of an open-source Policy Decision Point, Enforcement Point integrations, and a centrally managed Policy Administration Plane (Cerbos Hub) that coordinates unified policy-based authorization across your architecture. Enforce least privilege & maintain full visibility into access decisions with Cerbos authorization.
