Stay secure and audit-ready as AI enters production
Authorization for security leaders at regulated industries.
Security
Engineering
Compliance
Reduce hidden access risk
Remove fragmented, in-code authorization that creates blind spots and over-privileged access.
Control authorization logic
Define, approve, and update authorization policies in one place for users, services, and AI agents.
Know your AI blast radius
What can this AI agent access right now? Get a clear answer in seconds during incidents or regulatory deadlines.
“In fintech, you’ve got to track and enforce who can access data and when. If you don’t do this correctly, you potentially open up unauthorized access.”

Edgar Rivera, CTO
How authorization becomes your audit risk
Most enterprises can't answer the fundamental security question: "Who can access what, why, and when?".
Decision evidence is missing
Auditors demand proof of control across your systems. Without centralized evidence, compliance reviews fail and regulators issue fines.
Authorization gaps hide in your stack
One overlooked access path can become a breach that exposes customer data, triggers GDPR notifications, and damages your reputation.
Incident response stalls without visibility
When a breach happens, you can't quickly answer "What could this account access?" You miss the 48-hour notification window and regulators get involved.
Cerbos centralizes authorization and enforces Zero Trust
Cerbos consolidates fragmented authorization across your stack, giving you centralized control, real-time visibility, and decision-level proof for every access decision - human or AI.
Enforce the same authorization logic consistently across apps, APIs, services, non human identities, and AI workflows.
How Cerbos works
Fine grained, contextual, and continuous authorization for every layer of the software you build.
Free webinar
Your security stack has holes. Do you know where they are?
Applying aviation safety principles to Zero Trust Architecture.
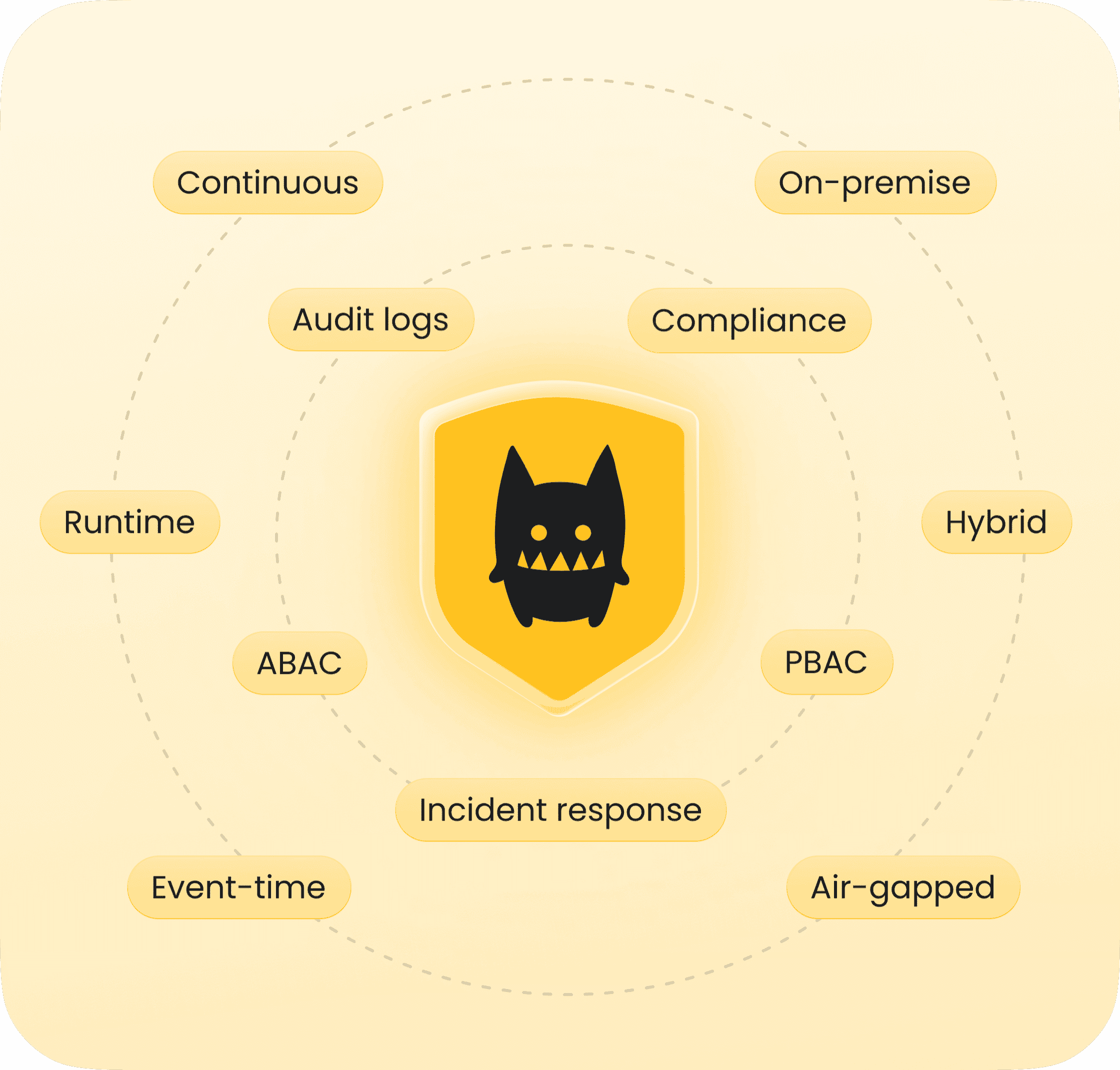
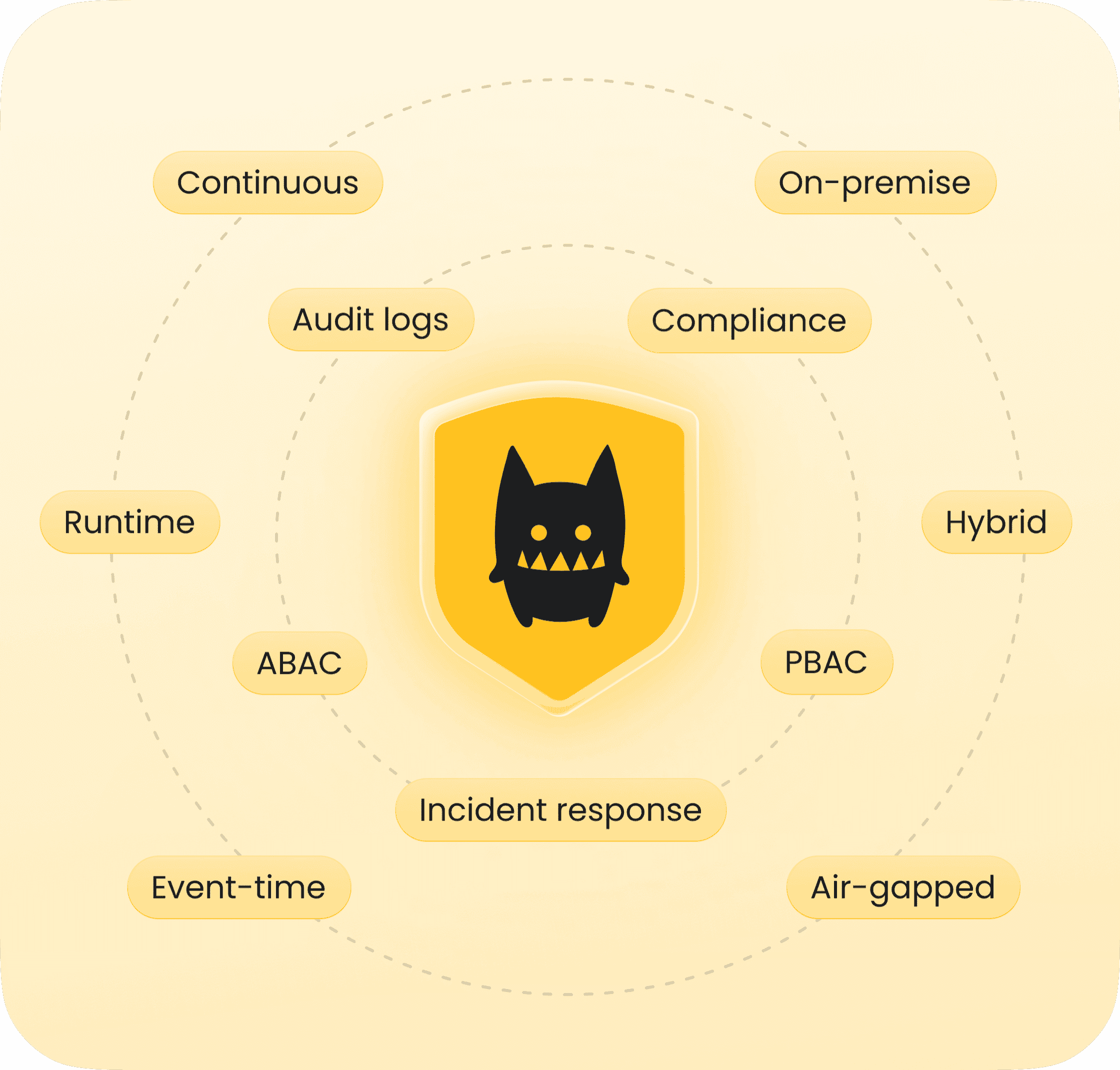
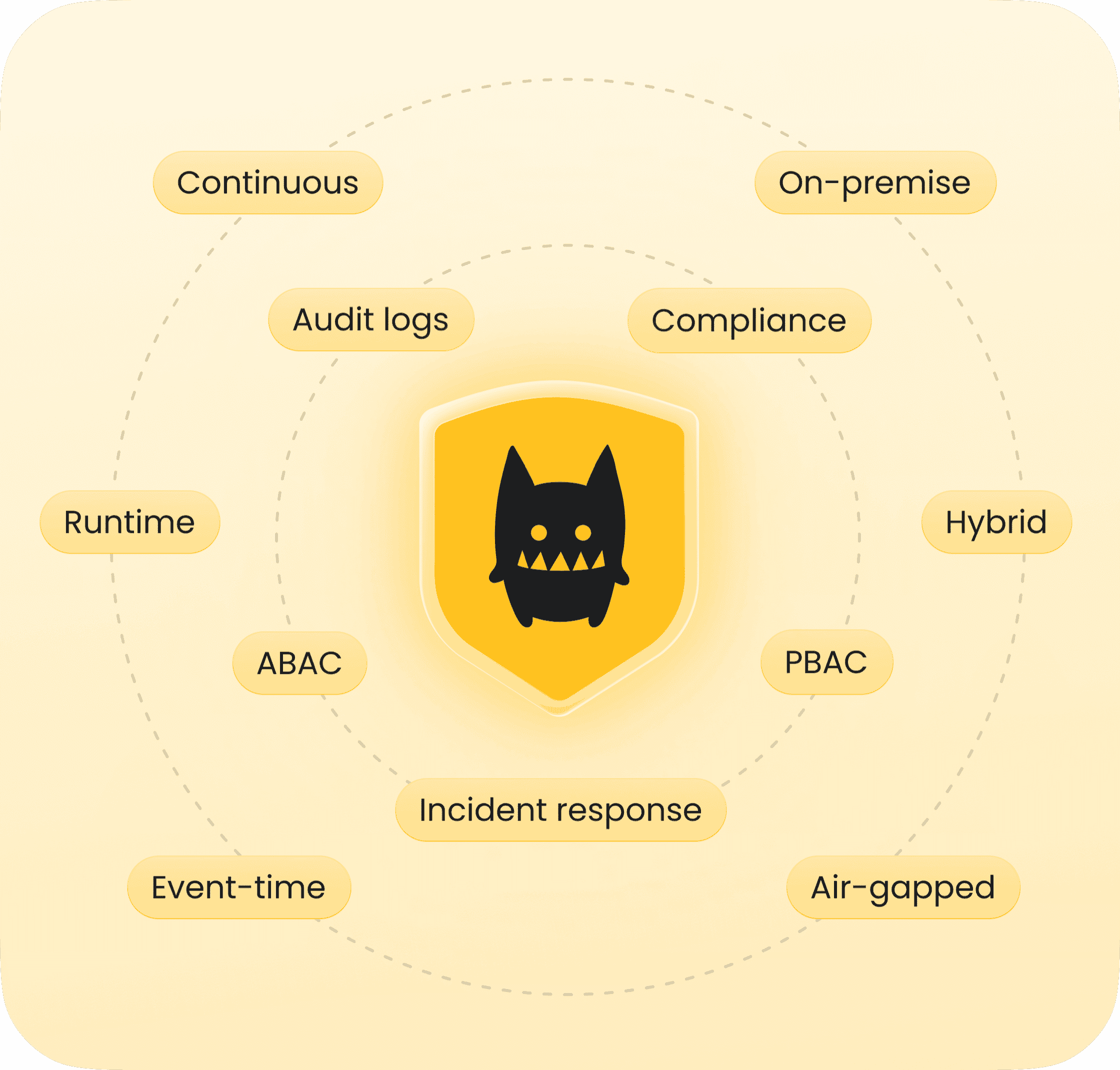
Access control for every use case
AI authorization
Enterprise app authorization
ABAC
RBAC
ReBAC
PBAC
Runtime
Event-time
Admin-time
Audit-time
Legacy systems
Cloud
Self-hosted
On-premise
Air-gapped
Compliance-ready with every decision
SOC 2 & 3
ISO 27001
PCI DSS

GDPR

HIPAA
FedRAMP
NIS2
DORA
How Utility Warehouse achieved continuous compliance across thousands of services and millions of NHIs with Cerbos.
SOC 2 & ISO audit-ready
AI agents secured
Threat detection
“We can trace every permission, investigate suspicious behavior, and answer questions about who did what, when, and why. We’ve gone from guesswork to forensic-level auditing across humans, machines, and everything in between.”


Rob Crowe
Principal Engineer, Utility Warehouse
Seamless integration
Authorization that fits your stack
Learn more about compliance, visibility, incident response and governance

Article
Protecting your own credibility as a security leader

Article
Staying compliant - What you need to know
Article
Dimmer switch: AI agent governance
Guide
5 authorization blind spots auditors find
Article
Zero trust has reached operational reality
Article
10 critical challenges CISOs face in 2026 and how to solve them

Checklist
The IAM security checklist for 2026
Guide
Learning Zero Trust from aviation - the Swiss Cheese model

Article
Overcoming IAM blind spots and fragmentation

Guide
Framework for evaluating authorization solutions
Article
CISO and architect’s guide to securing the new AI perimeter
Article
Stop trusting your employees. Uber's "God view" proves you can't

Ebook
How to adopt externalized authorization
Guide
Mapping business requirements to authorization policy
Article
Adaptive authentication and authorization
Ready to answer 'Who can access what?'
Our security engineers will show you how to get authorization evidence your auditors actually want to see.